The Framework Analysis of the Ethical Hacking Processes
Introduction
In a more digitalised world where cyberattacks are being advanced daily, ethical hacking has become a vital defence mechanism for organisations in all fields. Ethical hacking is a formal approach that is used to discover and resolve security vulnerabilities before they can be exploited by malicious actors. In contrast to criminal counterparts, ethical hackers (also referred to as the white hat hackers or penetration testers) work with the express permission to test the organisational defences through simulating the actual cyberattack scenarios.
The most recent industry statistics, from 2024, demonstrate the importance of this job. Over the year, security company “Citadelo” had conducted almost 500 penetration tests that revealed 2,820 web application, infrastructure, cloud services and mobile platform vulnerabilities. These results highlight an unpleasant fact: almost any system contains at least one medium-level vulnerability, which is why systematic ethical hacking has become one of the necessary elements of the current approach to cybersecurity.
The Five Phase Process Framework
Ethical hacking is a structured procedure divided into five phases that resemble the malicious hacker attack lifecycle. This systematic procedure will provide complete coverage without violating ethical standards and professionalism.
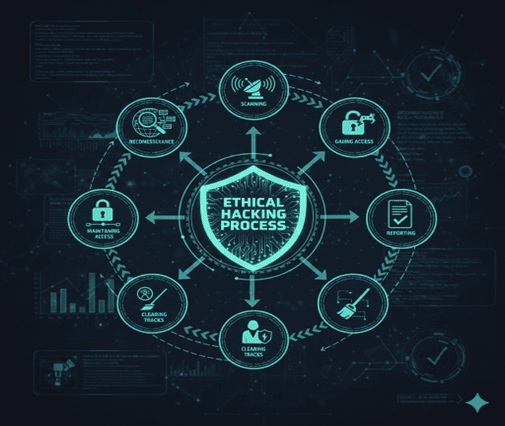
Phase 1: Reconnaissance
Reconnaissance forms the basis of any ethical hacking activity. At this phase, ethical hackers gather as much information as possible about their target through passive (typically researching public records, social media, and websites of the company) and active (applying network scanners to explore target systems) means. This is a process of gathering intelligence that assists in knowing the technological infrastructure of the organisation and the possible entry points.
Phase 2: Scanning and Enumeration
Scanning and Enumeration makes use of automated tools to conduct vulnerability testing to detect the presence of certain weaknesses in servers, applications, and network devices. Port scanning displays which services are available, and vulnerability scanners compare the systems found to databases of known security weaknesses. Network mapping develops a detailed topology of how the systems interact with each other and identifies future paths of lateral movement that can be used by attackers.
Phase 3: Gaining Access
Gaining Access is the most important phase of ethical hacking as here the simulated attack becomes a real one. Based on intelligence obtained during earlier stages, ethical hackers will seek to compromise security measures and illegally access target systems. They use several methods to take advantage of the vulnerabilities that have been detected, including exploiting unpatched software bugs to take advantage of lax authentication. After gaining access, the first thing the ethical hackers usually do is to perform privilege escalation, that is, to raise their access privileges beyond that of a regular user to that of an administrator.
Phase 4: Maintaining Access
Maintaining Access examines the capability of an organisation to identify continual threats. In the real world, attackers create persistence mechanisms to allow them to remain in the system, and ethical hackers also do the same by installing backdoors, creating disguised user accounts, or placing remote access tools. This stage proves the way attackers remain undetected in hacked systems.
Phase 5: Cleanup Tracks
Cleanup Tracks is the removal of evidence of the intrusion. On the side of an ethical hacker, logs in the system are altered or deleted, registry values are changed, and the tools that were used are removed. This proves the avoidance of attack investigation and tests the effectiveness of the organisation’s logging and monitoring tools.
Indian Cyberspace Security Situation
The digital transformation of India offers both new opportunities and huge challenges in cybersecurity. With 936 million internet users and fast digitisation pursuing the Digital India initiative, the country has turned into an ideal target of cyberattacks. In 2024, the statistics paint a sombre outlook of the threat landscape of Indian organisations.
There were massive data breaches in Indian vital sectors in 2024. BSNL was breached, exposing millions of users to a breach, and another giant breach happened, exposing the personal data of 750 million Indians, which is about 85% of the population. The 2024 Cost of a Data Breach report by IBM recorded the highest in the history of India, with the average amount spent on a data breach in India of INR 195 million (equivalent to about 2.35 million US dollars), a 39% increase over the prior year. The Indian Cyber Crime Coordination Centre showed a loss of INR 11,333 crore in cyber fraud in the first nine months of 2024.
The Indian government has realised these dangers and has put in place far-reaching cybersecurity programs, such as Cyber Surakshit Bharat, a capacity-building program for government departments. The CERT-In has 24×7 incident response services, and the Digital Personal Data Protection Act of 2023 stipulated legal mechanisms to protect data. The government is focused on educating 500,000 cybersecurity professionals in five years, which is an urgent demand for qualified ethical hackers.
The broadening of this attention has presented immense opportunities to ethical hackers in India. Key personalities such as Anand Prakash have been featured in the Forbes 30 Under 30 Asia list because of identifying thousands of weaknesses in the big tech platforms. According to the 2024 Global Digital Trust Insights Survey conducted by PwC, 99% of Indian organisations intend to escalate their budgets on cybersecurity, and 52% of them are most worried about threats to the cloud.
Developed Frameworks and New Trends
Although the five-stage model provides a robust framework, the current-day ethical hacking has developed to adapt to a more advanced framework. The TIBER-EU framework of the European Central Bank is an important development, especially when it comes to important financial infrastructure. In 2024, modified to reflect the Digital Operational Resilience Act, TIBER-EU is not a traditional penetration testing as it starts with a threat intelligence analysis that is specific to the organisation and industry.
Although cybersecurity is becoming more and more automated, human expertise cannot be replaced. Accomplished ethical hackers also often find turnkey attack chains by chaining together several smaller vulnerabilities that would be flagged by automated tools singly. The Caffe Latte attack and the WEP cloaking breaking were brought forward by an ethical hacker, Vivek Ramachandran, to the Indian context and are taught in wireless security textbooks across the world.
In the future, the power of artificial intelligence and machine learning is increasing, which facilitates the speed of vulnerability identification for ethical hackers. Emerging frontiers that are turning the role of the ethical hacker into that of not an outside auditor, but as a collaborative partner, are cloud security, IoT device testing, and the DevSecOps movement, which incorporates security testing across the development lifecycle.
Conclusion
The systematic framework that is availed by ethical hacking processes is the one that can enable the determination and fixation of vulnerabilities in security that are susceptible to exploitation by bad actors. In India, the case is an example of the significance of ethical hacking in the world. As the cost of data breaches is at an all-time high and the infrastructure is continuously being compromised, the country has a cybersecurity issue that is similar to the one facing other countries around the globe.
The use of skilled ethical hackers is accelerating as the cyber threat is becoming more advanced and the skills gap is increasing. It is companies that invest in rigorous, structure-based ethical hacking that develop resiliency to resist future, sophisticated threats. The development of the field proves a simple fact: good cybersecurity must be actively and constantly tested by the competent professional who should be able to think as an attacker, but act as a defender.
References
[1] Citadelo, “Ethical Hacking Report 2024: Vulnerabilities Unveiled,” 2024. [Online].
Available: https://citadelo.com/en/blog/ethical-hacking-report-2024
[2] European Central Bank, “TIBER-EU Framework updated to align with DORA,” 2025. [Online].
Available: https://www.ecb.europa.eu/press/intro/news/html/ecb.mipnews250211.en.html
[3] IBM India, “IBM Report: Escalating Data Breach Disruption Pushes Average Cost of a Data Breach in India to All-Time High of INR 195 Million in 2024,” Jul. 2024. [Online].
Available: https://in.newsroom.ibm.com/2024-07-31-IBM-Report
[4] Press Information Bureau, Government of India, “India launches first Digital Threat Report 2024 to support cybersecurity in the BFSI sector,” 2024. [Online].
Available: https://www.pib.gov.in/PressReleasePage.aspx?PRID=2119801
[5] PwC India, “Cybersecurity In India: 2024 Global Digital Trust Insights Survey,” 2024. [Online].
Available: https://www.pwc.in/digital-trust-insights-india.html
[6] 63SATS Cybertech, “India’s Major Cybersecurity Incidents of 2024: What Lies Ahead in 2025,” 2025. [Online].
Available: https://63sats.com/blog/indias-major-cybersecurity-incidents-of-2024
[7] DNA India, “Top 10 Ethical Hackers in India,” 2024. [Online].
Available: https://www.dnaindia.com/technology/report-top-10-ethical-hackers-in-india-3102189
[8] Internet Freedom Foundation, “IFF’s cybersecurity report for the third quarter of 2024,” 2024. [Online].
Available: https://internetfreedom.in/iffs-cybersecurity-report-for-the-third-quarter-of-2024/
Common Ethical Hacking FAQ
- What is the goal of this process?
The goal is to provide a structured methodology for identifying vulnerabilities. - Why is ethical hacking essential?
It allows organizations to stay ahead of cybercriminals by simulating real-world attacks. - How many phases are in the standard framework?
The standard framework consists of five distinct phases. - What occurs during reconnaissance?
In this initial stage, practitioners gather intelligence on the target’s digital footprint. - Is the five-phase model the only one used?
No, modern ethical hacking often adopts advanced structures like TIBER-EU. - What is passive reconnaissance?
It involves gathering public data without direct interaction with the target systems. - How does scanning benefit the process?
Scanning allows the practitioner to identify open ports and specific software weaknesses. - What does “Gaining Access” involve?
This is the phase where the attacker attempts to exploit weaknesses to enter the system. - Why is it important to maintain access?
This tests how long a persistent threat can remain undetected by an organization. - What is “Cleanup Tracks”?
This is the removal of evidence of the intrusion to test logging tools. - How is the Indian cybersecurity landscape changing?
India has become a key hub for professionals to protect critical infrastructure. - What is the Digital India initiative’s impact?
Rapid digitization has increased the “attack surface,” making a robust security framework necessary. - Are there legal protections in India?
Yes, the Digital Personal Data Protection Act of 2023 provides a legal framework for data. - Who are famous Indian practitioners?
Experts like Anand Prakash have gained global recognition in the ethical hacking field. - What is the TIBER-EU model?
It is a threat-intelligence-led approach designed for the European financial sector. - How does AI impact the future?
AI is being used to automate vulnerability detection and speed up analysis. - Can these methods prevent all attacks?
No system is 100% foolproof, but systematic ethical hacking significantly reduces risk. - What is privilege escalation?
It is a technique used to raise user permissions to an administrative level. - Why is the “human element” vital?
Automated tools miss complex attack chains human intuition remains a critical component. - How can I start learning this framework?
Most beginners start by learning the five phases of the framework via certifications.
Penned by Arya
Edited by Anuj Kumar, Research Analyst
For any feedback mail us at [email protected]
Streamline Your Hiring with Eve Placement’s Custom Assessments
Eve Placement helps you engage, assess, and recruit top talent through tailored hiring challenges that go beyond resumes. From technical quizzes and real-world case studies to psychometric evaluations and audio/video submissions, our platform enables smarter, data-driven hiring decisions. Advanced security features ensure authenticity and eliminate fraud, giving you reliable results. Ready to hire better? Know More.
Mail us at [email protected]
