Key Compliance Lessons from Recent Cyberattacks
Article: Cybersecurity risk assessment
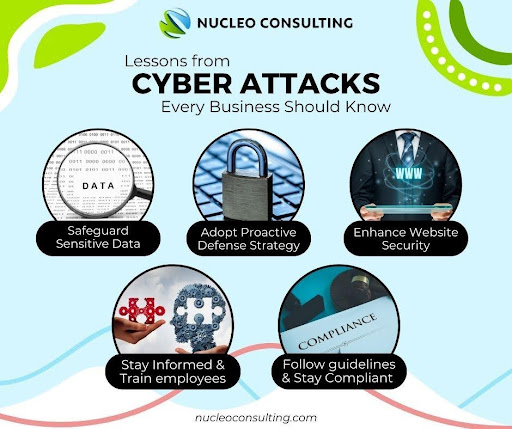
In today’s online-based world, no company is safe from the risk of cyberattacks. From small start-ups to large corporations, Online attacks can stop work, show private data, and harm a company’s public image. But with every big attack, there are useful lessons to learn lessons that help companies create stronger, more rule-following setups. This article presents a detailed cybersecurity incident review and outlines seven crucial cyberattack compliance lessons that every business must understand and implement.
- Regular Risk Assessments Are Non-Negotiable
Many companies only understand their safety problems after an attack. Doing regular safety checks helps you find weak points early and use safety steps before an attack happens. Safety checks must be included in your 3-month or yearly rule-following list.
- Train Employees – Human Error Is Still the #1 Cause
In most major data breaches, human error is a leading cause. Employees clicking phishing emails, using weak passwords, or ignoring basic security protocols are common issues. Cyberattack Compliance Lesson: Include mandatory cybersecurity training in your compliance program for all employees.
- Incident Response Plans Must Be Tested – Not Just Documented
Many firms have an incident response plan, but few have tested it. During a real attack, the absence of a rehearsed plan leads to confusion, delays, and legal trouble. Cybersecurity Incident Review Tip: Simulate a cyberattack once a year to test your team’s readiness.

- Vendor Management Is Critical
The latest online attacks have shown that outside suppliers can be the easiest target. If your business helpers don’t follow the rules, then you are also not rule-following. Key Lesson: Ensure all vendors follow the same compliance standards you enforce internally.
- Data Encryption Is a Must – Not a Choice
Hackers often exploit unencrypted data. Despite being a basic security practice, many businesses still store sensitive data in plain text. Cyberattack Compliance Lesson: Encrypt all sensitive customer and employee data, both at rest and in transit.
- Compliance Documentation Saves You Legally
In several high-profile attacks, companies that had clear compliance logs and updated security documentation were able to defend themselves in court or avoid heavy fines. Cybersecurity Incident Review Insight: Maintain up-to-date compliance logs and keep backup records off-site.
- Don’t Ignore Government Guidelines
Rule-making groups like SEBI, CERT-IN, and RBI often give new rules about online safety and must-follow steps. Key Lesson: Keep yourself updated and match your rule-following actions with the latest country-wide or business area rules.
Conclusion
Online attacks are no longer just computer problems; they are also rule, law, and public image problems. By learning from past attacks and using these seven lessons, companies can make their protection stronger, keep following the rules, and protect people’s trust. Remember: Stopping early is always better than fixing problems later. Act now, before you become the next news story.
10 FAQs on Cybersecurity Risk Assessment
1. What is a cybersecurity risk assessment?
A cybersecurity risk assessment is the process of identifying, analyzing, and evaluating potential threats to an organization’s digital assets and systems.
2. Why is cybersecurity risk assessment important for businesses?
Cybersecurity risk assessment helps businesses understand vulnerabilities, prioritize threats, and implement effective security measures to prevent data breaches.
3. How often should a cybersecurity risk assessment be conducted?
Experts recommend conducting a cybersecurity risk assessment at least annually, or more frequently if there are major system changes or emerging threats.
4. What are the key components of a cybersecurity risk assessment?
Key components include asset identification, threat analysis, vulnerability assessment, impact evaluation, and mitigation planning.
5. Who should perform a cybersecurity risk assessment?
Cybersecurity risk assessments can be performed by internal IT teams, external consultants, or specialized cybersecurity firms.
6. What tools are used in cybersecurity risk assessment?
Common tools include vulnerability scanners, penetration testing software, compliance checklists, and risk management platforms.
7. Can small businesses benefit from cybersecurity risk assessment?
Absolutely. Cybersecurity risk assessment is crucial for small businesses to protect customer data and avoid costly breaches.
8. How does cybersecurity risk assessment support compliance?
Cybersecurity risk assessment ensures that organizations meet regulatory requirements such as GDPR, HIPAA, and ISO 27001.
9. What are the consequences of skipping cybersecurity risk assessment?
Skipping cybersecurity risk assessment can lead to data breaches, financial loss, legal penalties, and reputational damage.
10. Is cybersecurity risk assessment required by law?
In many industries, cybersecurity risk assessment is a legal requirement under data protection and privacy regulations.
References
[1] “Cybersecurity Best Practices for Businesses,” National Cyber Security Centre. [Online]. Available: https://www.ncsc.gov.uk/guidance
[3] https://www.nucleoconsulting.com/key-lessons-from-5-cyber-attacks-every-business-should-know/
Penned by Anjum Mulani
Edited by Shashank Khandelwal, Research Analyst
For any feedback mail us at [email protected]
Streamline Your Hiring with Eve Placement’s Custom Assessments
Eve Placement helps you engage, assess, and recruit top talent through tailored hiring challenges that go beyond resumes. From technical quizzes and real-world case studies to psychometric evaluations and audio/video submissions, our platform enables smarter, data-driven hiring decisions. Advanced security features ensure authenticity and eliminate fraud, giving you reliable results. Ready to hire better? Know More.
Mail us at [email protected]
