Public Key Infrastructure (PKI) and Digital Certificates
Introduction
Public Key Infrastructure (PKI) is one of the most utilized sets of entities to authenticate data on the internet. It is used to secure and verify communications between browsers and servers. It also makes access to devices secure.
But the two primary goals of PKI are to
keep messages private and
verify the sender’s identity
Essentially, PKI uses cryptographic public keys that are linked to digital certificates.
But What are these Digital Certificates?
A digital certificate is like an ID card that is issued by a competent authority which contains details of an individual or property and further, cannot be
tampered with. It verifies a person’s identity and is traceable. These certificates also have an expiration date.
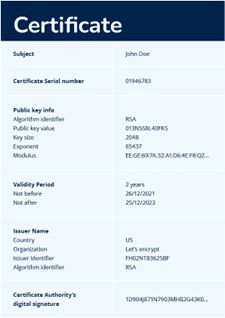
An Example of Digital Certificate
As mentioned earlier, digital certificates are issued by authorities called Certification Authorities (CA).
Before a certificate is issued, the CA, along with a Registration Authority (RA), cross-checks the identity of the person or organization requesting the certificate to ensure secure internet usage.
Some of the details that are included in a digital certificate are:
The identity of the certificate’s owner
The owner’s public key
The certificate’s validity period
The trusted authority that issued the certificate
The digital signature of the certificate’s issuer
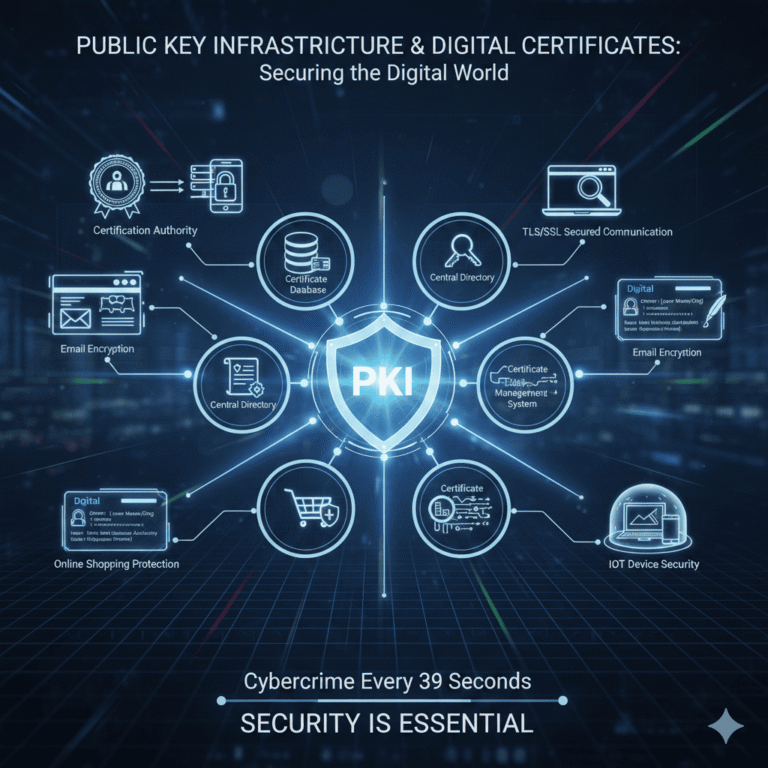
Moving on, the main parts of Public Key Infrastructure include the following:
The certificate database acts as a storage place for digital certificates and their metadata, including their validity period.
The central directory is where cryptographic keys are stored securely.
The certificate policy describes how PKI works and can be reviewed by others for authentication.
The certificate management system handles the delivery of certificates.
Why is PKI Used?
One of the most common uses of PKI is TLS/SSL (Transport Layer Security/Secure Sockets Layer), which protects encrypted HTTP communications.
And to get a certificate for an entity or website, the owner must prove their identity, which is further verified by the CA and RA. Once the authentication is confirmed, the website owner can purchase an SSL certificate and install it on their web server, so the visitors of the website know the legitimacy of the website.
PKI is also used for:
Encrypting and verifying emails
Signing documents and software
Securing internal communications on database servers
Protecting web communications like online shopping
Authenticating and encrypting documents
Securing local networks and smart card authentication
Controlling access to VPNs and company networks
Securing communication between trusted devices, such as IoT devices
The Role of Digital Certificates in PKI
The primary duty of PKI is to manage cryptographic keys by issuing and managing digital certificates, also famously known as X.509 certificates and PKI certificates. The easiest way to comprehend the process of how PKI manages digital certificates is to think of it as being analogous to a digital DMV. Just like the Department of Motor Vehicles (DMV), PKI brings in a third party to assign identities to digital certificates, which is the RA, which is trusted and legitimate. And just like driver’s licenses, digital certificates are hard to forge and include details about the owner along with a set expiration date.
Conclusion
Public key infrastructure has become an important part of our daily tech life. Digital certificates which are an inherent part of them also secures connection and data which is needed in the world where cybercrime occurs every 39 seconds. Thus, security is necessary and essential and shall not be taken lightly.
References
[1] DigiCert, “What is Public Key Infrastructure (PKI)?,” 2025. [Online].
Available: https://www.digicert.com/what-is-pki
[2] GlobalSign, “Digital Certificates and PKI Explained,” 2025. [Online].
Available: https://www.globalsign.com/en/learn/pki-digital-certificates
[3] Entrust, “Public Key Infrastructure (PKI) Overview,” 2024. [Online].
Available: https://www.entrust.com/resources/pki-overview
[4] Sectigo, “The Role of Digital Certificates in Cybersecurity,” 2025. [Online].
Available: https://sectigo.com/resource-library/digital-certificates
[5] Thales, “PKI and Certificate Management Best Practices,” 2024. [Online].
Available: https://cpl.thalesgroup.com/encryption/pki-certificates
Securing the Web: Essential FAQs on PKI and Certificates
- What does PKI stand for?
It stands for Public Key Infrastructure, a framework used to secure data. - Why is identity verification important in this system?
Verifying a sender’s identity ensures that the data is coming from a legitimate source and not an imposter. - What is the primary role of a Digital Certificate?
It acts as an electronic “ID card” to prove the ownership of a public key. - Who issues these certificates?
They are issued by a Certification Authority (CA). - How does an RA assist the CA?
The Registration Authority (RA) verifies the identity of the requester before the CA issues the certificate. - What is the difference between a public key and a private key?
Public keys are shared openly, while private keys are kept secret by the owner. - How does PKI protect my emails?
It uses encryption to ensure only the intended recipient can read the message. - What is an X.509 certificate?
This is the standard format used for most certificates within a PKI setup. - Can a digital certificate expire?
Yes, they include an expiration date to ensure security remains current. - How does the system prevent tampering?
Digital signatures are used to ensure the certificate has not been altered since issuance. - What is the “central directory” in this framework?
It is a secure storage location for cryptographic keys. - Is PKI used in online shopping?
Yes, it secures the HTTP communications (HTTPS) for credit card transactions. - How does it help with VPNs?
It authenticates the identity of users attempting to access a private company network. - What is a “Certificate Policy”?
It is a document describing how the infrastructure functions and the security levels it provides. - Can certificates be used for software?
Yes, developers use them to sign software so users know the code hasn’t been modified. - How often does cybercrime occur?
According to current statistics, a cyberattack occurs roughly every 39 seconds. - What is the role of a certificate database?
It stores the certificates and their associated metadata for easy retrieval. - Is this technology used in IoT devices?
Yes, it secures communication between smart devices like thermostats and cameras. - How does a website owner get a certificate?
They must prove their identity to a CA/RA and then install the issued file on their server. - What is the main goal of the infrastructure?
The main goals are to keep messages private and verify the identity of the participants.
Penned by Aarushi
Edited by Anuj Kumar, Research Analyst
For any feedback mail us at [email protected]
Streamline Your Hiring with Eve Placement’s Custom Assessments
Eve Placement helps you engage, assess, and recruit top talent through tailored hiring challenges that go beyond resumes. From technical quizzes and real-world case studies to psychometric evaluations and audio/video submissions, our platform enables smarter, data-driven hiring decisions. Advanced security features ensure authenticity and eliminate fraud, giving you reliable results. Ready to hire better? Know More.
Mail us at [email protected]
